Security & Access
The Trust Layer
of your Business.
The secure bunker that builds trust with engineers & customers.
What is the Privacy Labs Trust Layer?
12 security check-points serve as a digital bunker, utilising pattern-based defence to detect threats like credential stuffing and unauthorised access before they escalate. We anchor your fiduciary accountability with SHA-256 hashed audit logs, providing the ‘bulletproof’ evidence required to prove ‘reasonable security safeguards’ under Section 8(5).
Book a demo →Incident response minus the operational chaos
Privacy Labs takes your engineering team through a systematic & smooth workflow that ensures every incident is reported before it escalates into a penalty.
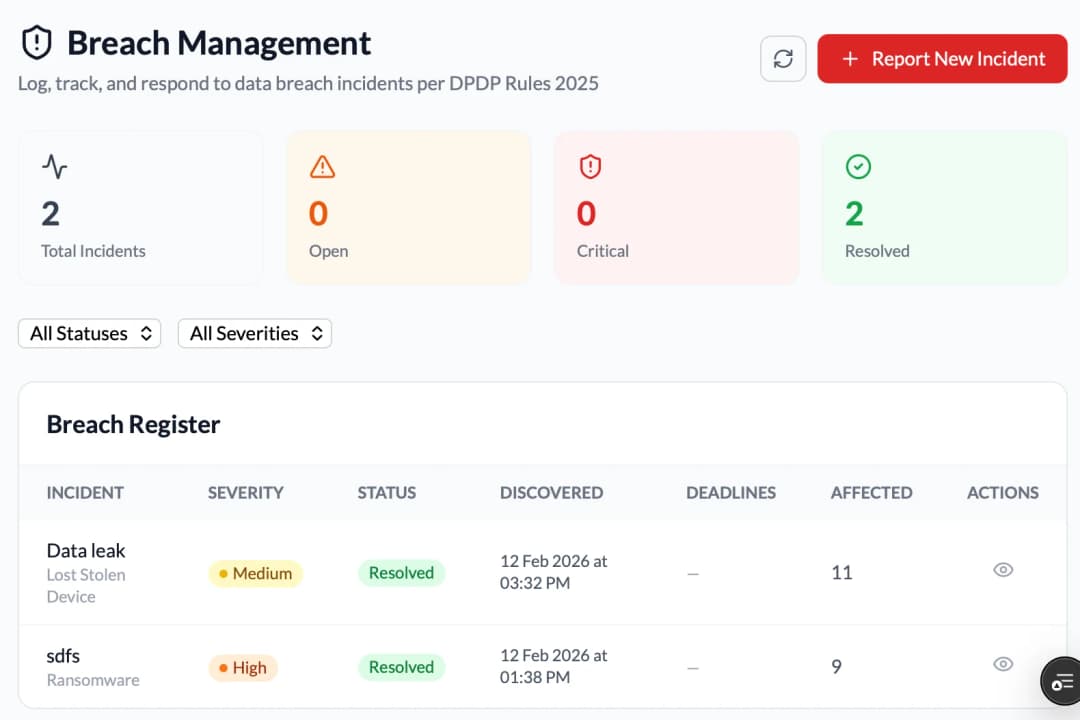
Breach Dashboard & Lifecycle Tracking
A high-level command centre to track the real-time status of all security incidents
6 Stage Lifecycle Tracking
Manage incidents through a visual command centre: Detected → Assessing → Contained → Notified → Resolved → Closed
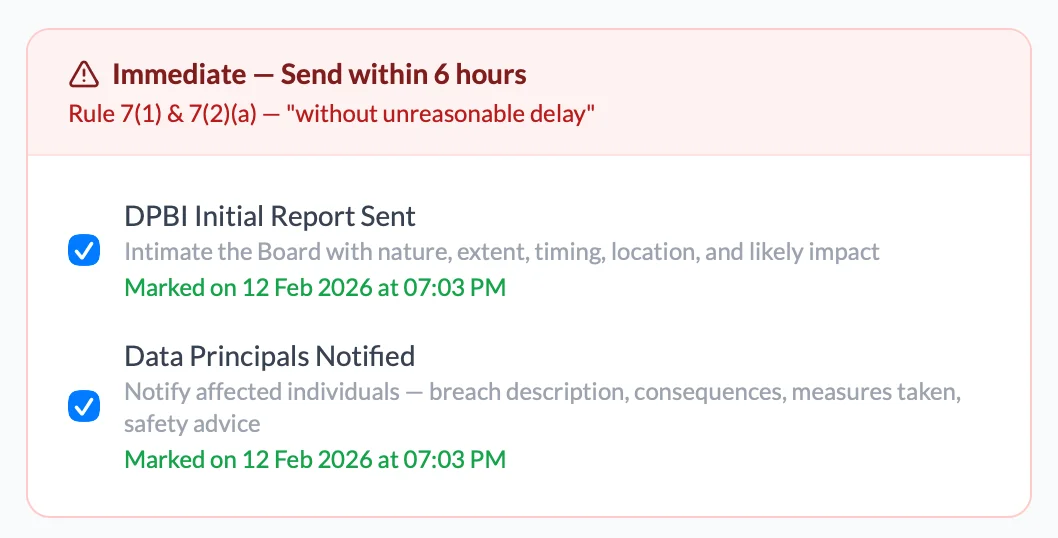
Automated DPBI Reporting
Pre-configured regulatory notes & principal notices with timers for mandated Initial Report (in 6 hrs) and Detailed Report (in 72 hrs)
Breach Register & Incident Overview
A centralised ledger documenting the nature, extent, and likely impact of the breach for "Audit-Ready" evidence
Immutable Response Timeline
A timestamped, non-editable timeline & audit trail of every breach mitigation step and team action taken during the response
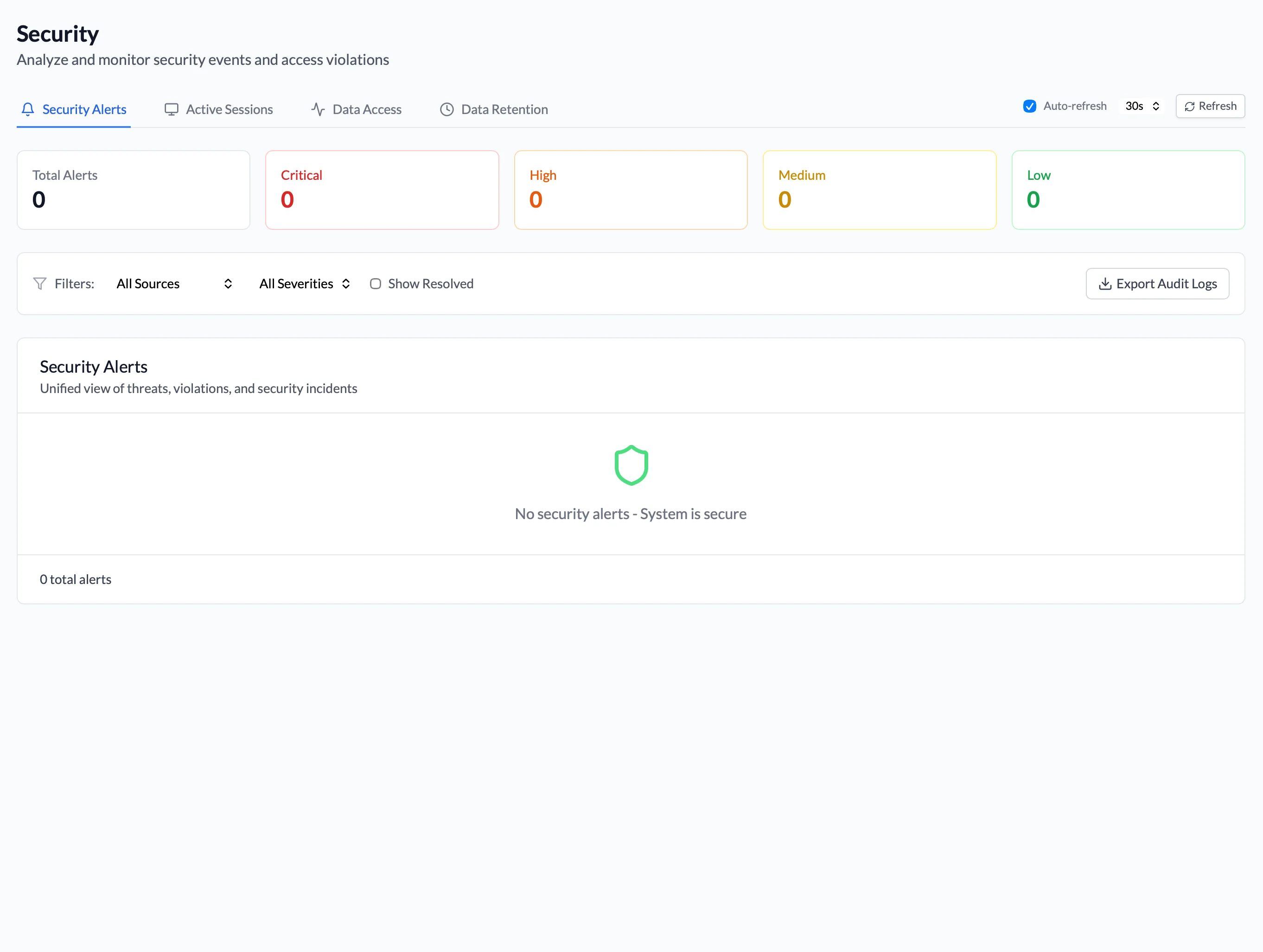
Beyond Mandated Security. Detect threats and react powerfully.
In the era of automation-led security threats, any company's data is valued very highly. Our platform goes beyond prescribed security, identifying and scoring threats before they escalate.
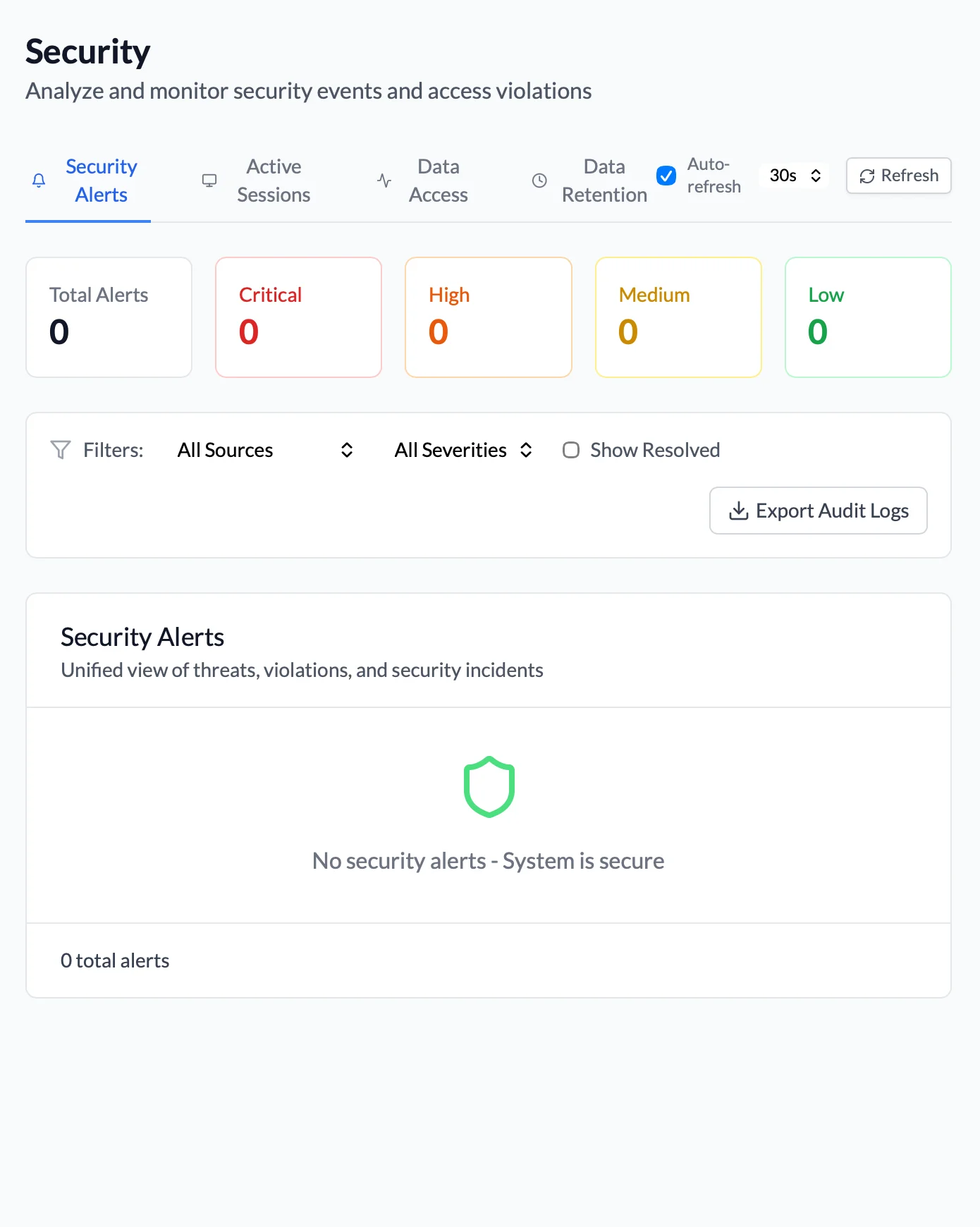
Real-time Contextual Threat Alerts
Instant notifications to your team in the event of suspicious patterns & unusual spikes
Pattern-based Defence
A Threat-Detection engine connects the dots to identify & classify manipulation
Unauthorised Access Monitoring
Identification of privilege escalation and unauthorised cross-organisation access
Technical Safeguard Verification
Real-time checks for 'Encryption at rest' and SSL/TLS connectivity
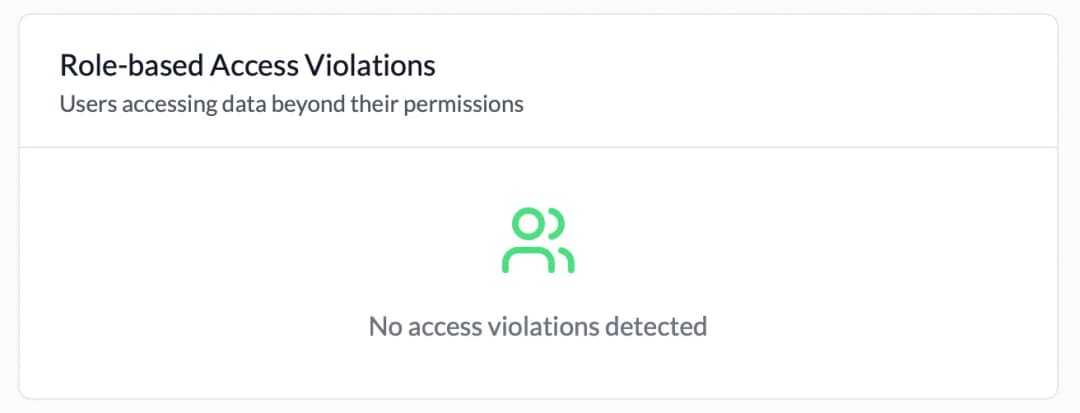
Granular Permission Management for your most sensitive data
Access-management is complex in teams of any size; our platform monitors access, logs activity and sends alerts whenever incidents occur.
4 Distinct Roles
Users are classified simply into: Admin, DPO, Auditor, and Operator
Access Violation Tracking
Monitoring & reporting of instances when users attempt to access data beyond permissions
Intelligent Operator Restrictions
Operators see only their assigned tasks, limiting their access within your database
Data Access Activity Log
Time-stamped feed of specific team actions like exports, views etc.
Multi-factor Authentication
2FA at the time of login via OTP or approve a notification
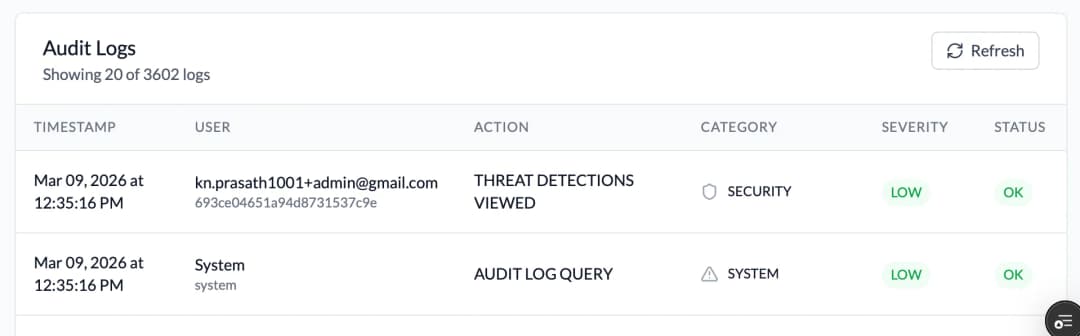
Bullet-proof Compliance Evidence. For every system action.
Want to prove your compliance? One-click exports are the answer. Every request goes through many security layers & an encrypted audit log records every action.
SHA-256 Hashed Audit Logs
Every system action is recorded in a tamper-proof format, serving as your primary defence during a Board inquiry
Zero-Configuration Protection
Out-of-the-box prevention against XSS, NoSQL injections, and CSRF with constant-time token comparison
Intelligent Rate Limiting
Built-in safeguards to prevent API abuse and ensure system availability
Quick Export for Audit
One-click filtering and export of logs (PDF, CSV, JSON) for legal and regulatory review